How to Install WeKan with LEMP Stack on Rocky Linux 9
WeKan ® is a completely Open Source and Free software collaborative kanban board application with an MIT license. Whether you’re maintaining a personal to-do list, planning your holidays with some friends, or working in a team on your next revolutionary idea, Kanban boards are an unbeatable tool to keep your things organized.
They give you a visual overview of the current state of your project and make you productive by allowing you to focus on the few items that matter the most. In this article, we are going to learn how to install WeKan on Rocky Linux 8. So, let’s get started.
Checkout the WeKan Project Here.
Try this wiki on our VPS. Starting at just $5/month with 24x7 In-house customer support.
Pre-requisites :
-
A system with Rocky Linux 9 installed and running.
-
rootaccess to the system. - LEMP Stack installed and running, for this, you can refer to one of our guides on installing the LEMP Stack (Nginx, MariaDB, and PHP).
Once you're all set, we'll proceed with WeKan installation and configuration.
To Install snapd
Let us begin with installing snapd. For installing snapd, use the below commands
dnf install snapd
systemctl enable --now snapd.socket
ln -s /var/lib/snapd/snap /snap Install Let’s Encrypt SSL Certificate
Let's issue an SSL certificate for the domain. For this, we will need the EPEL repository and the mod_ssl package on Rocky Linux 8 operating system.
Update and install EPEL repository and the mod_ssl package on the system using the below command:
dnf install epel-release mod_ssl -yNext, we will install the certbot client which is used to create Let's Encrypt certificates:
dnf install python3-certbot-nginx -yInstall SSL Certificate
Use the certbot command to issue a Let's Encrypt certificate. Replace dev.domainhere.info and dev@dev.domainhere.info with your domain name and email :
certbot --nginx --agree-tos --redirect --hsts --staple-ocsp --email dev@dev.domainhere.info -d dev.domainhere.infoSSL certificates are valid for 90 days. The renewal process is now automated, you do not have to renew this manually.
Configuring Nginx Reverse Proxy
Let's configure nginx.conf with the following command:
nano /etc/nginx/nginx.confCopy below code to nginx.conf file.
# For more information on configuration, see:
# * Official English Documentation: http://nginx.org/en/docs/
# * Official Russian Documentation: http://nginx.org/ru/docs/
user nginx;
worker_processes auto;
error_log /var/log/nginx/error.log;
pid /run/nginx.pid;
# Load dynamic modules. See /usr/share/doc/nginx/README.dynamic.
include /usr/share/nginx/modules/*.conf;
events {
worker_connections 1024;
}
http {
log_format main '$remote_addr - $remote_user [$time_local] "$request" '
'$status $body_bytes_sent "$http_referer" '
'"$http_user_agent" "$http_x_forwarded_for"';
access_log /var/log/nginx/access.log main;
sendfile on;
tcp_nopush on;
tcp_nodelay on;
keepalive_timeout 65;
types_hash_max_size 2048;
include /etc/nginx/mime.types;
default_type application/octet-stream;
# Load modular configuration files from the /etc/nginx/conf.d directory.
# See http://nginx.org/en/docs/ngx_core_module.html#include
# for more information.
include /etc/nginx/conf.d/*.conf;
}Now, type in Ctrl+O and type Ctrl+X to save and exit the file.
Create a new Nginx configuration file dev4.conf for the domain with the following command:
vi /etc/nginx/conf.d/dev.confAdd the following codes:
Replace
dev.domainhere.infoand192.169.7.180withYour Domain Name & IP Addressalso Change SSL Path according to your SSL Path.
upstream app {
server 192.169.7.180:3001;
}
server {
listen 80 default_server;
server_name dev.domainhere.info;
return 301 https://$server_name$request_uri;
}
server {
listen 443 ssl; # managed by Certbot
# The host name to respond to
server_name dev.domainhere.info;
ssl_certificate /etc/letsencrypt/live/dev.domainhere.info/fullchain.pem; # managed by Certbot
ssl_certificate_key /etc/letsencrypt/live/dev.domainhere.info/privkey.pem; # managed by Certbot
include /etc/letsencrypt/options-ssl-nginx.conf; # managed by Certbot
ssl_dhparam /etc/letsencrypt/ssl-dhparams.pem; # managed by Certbot
location / {
proxy_pass http://app;
proxy_set_header X-Real-IP $remote_addr;
proxy_set_header X-Forwarded-For $remote_addr;
proxy_set_header Host $host;
proxy_set_header X-Real-Port $server_port;
proxy_set_header X-Real-Scheme $scheme;
}
}Now, press the Esc key, and type :wq! and press the Enter key to save and exit the file.
Now, restart & check the Nginx with the following commands:
For SELinux enabled systems, Run the below command
setsebool -P httpd_can_network_connect 1Restart Nginx Server
systemctl restart nginx
systemctl status nginx Enable http and https ( 80/443/3001 ):
To enable http and https connection through the firewall, follow the commands:
firewall-cmd --zone=public --permanent --add-port 80/tcp
firewall-cmd --zone=public --permanent --add-port 443/tcp
firewall-cmd --zone=public --permanent --add-port 3001/tcp
firewall-cmd --reload Install WeKan using Snapd
Let's install Wekan using the below commands
snap install wekan
snap set wekan root-url="https://dev4.domainhere.info"
snap set wekan port='3001'
systemctl restart snap.wekan.mongodb
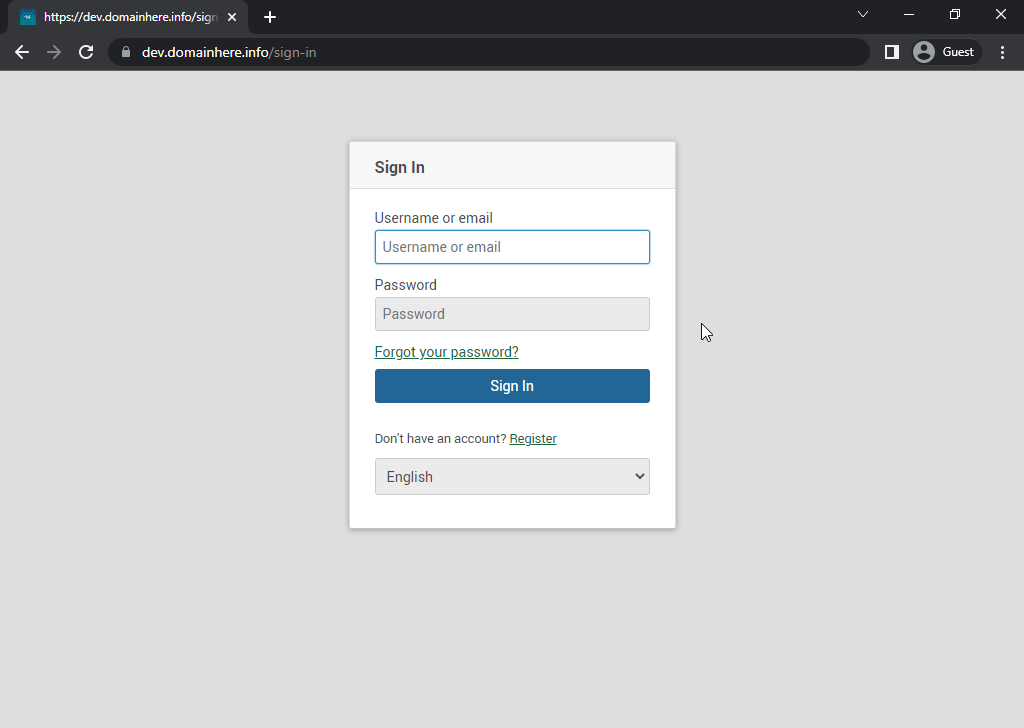
systemctl restart snap.wekan.wekan Accessing WeKan
Now open the IP address from your browser, this will redirect you to the Wekan.
https://dev.domainhere.info/sign-inReplace the
dev.domainhere.infowith the actual IP or domain configured on the server.
Input the Database details which was configured earlier. Follow the below steps:
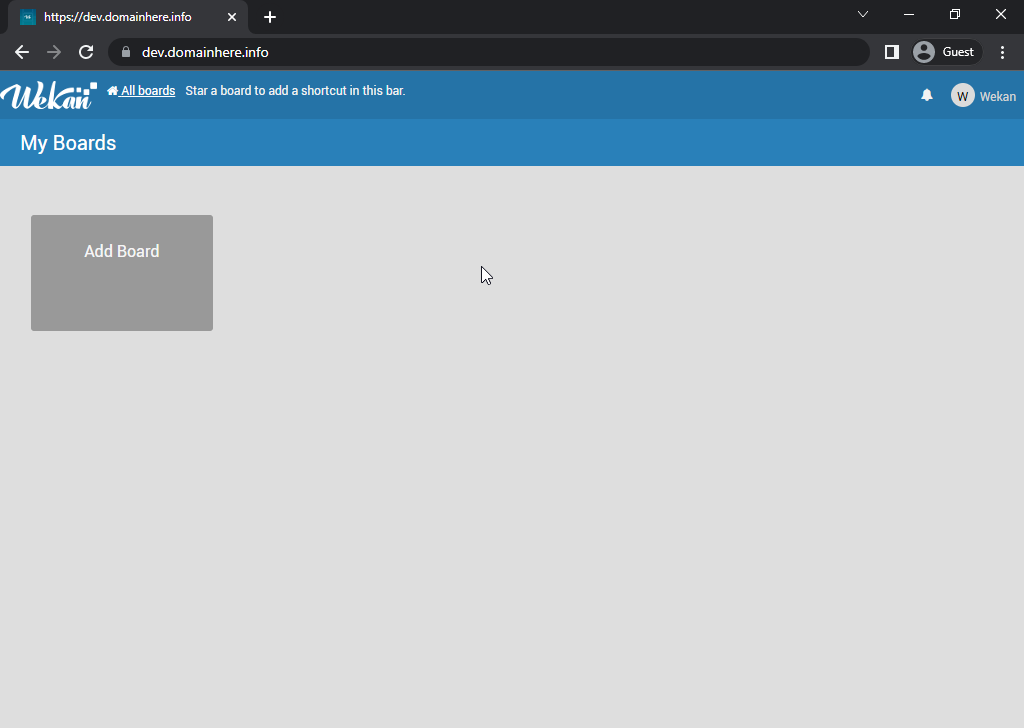
Now you have successfully installed WeKan with LEMP Stack on Rocky Linux 9.
CrownCloud - Get a SSD powered KVM VPS at $4.5/month!
Use the code WELCOME for 10% off!
1 GB RAM / 25 GB SSD / 1 CPU Core / 1 TB Bandwidth per month
Available Locations: LAX | MIA | ATL | FRA | AMS